NSE : Nmap Scripting Engine
Learn how Nmap Scripting Engine (NSE) works, its architecture, script categories, and real vulnerability scanning examples. It is a Lua-powered scripting engine that runs advanced pre-built and custom-written scripts to enhance network scanning and security analysis.
NSE (Nmap scripting engine), is the more advanced and useful version of Nmap that is utilized for actual reconnaissance and security verification.
Basic Nmap tells us which ports are open, but NSE explains what those open ports actually mean in practice.
By enabling logic-based, task-specific scripts to run directly against discovered services, NSE expands on the drawbacks of conventional scanning. NSE automates that thought process and applies it uniformly across hosts, eliminating the need to manually test each service individually. For Detailed information visit NMAP NSE official documentation.
Internal Working of NSE
Before Deep dive in NSE, we have to study internal working methods of NSE for better understanding. There are several parts in which the working is divided. These parts are called phases of NSE.
1. First Phase of NSE
The phase 1 gather the basic information about the host, It scans the target to figure out what’s alive, which ports are open, and what services are running which ports and services are active. Basically it scans the overall host and generate the relevant information from it.
This step is important because, without this information, running scripts would be blind and inefficient.
2. Second Phase of NSE
The result of First Phase scan, it decide what’s worth testing. And based on what the user asks for (like default or vulnerability scripts), NSE checks its internal script database and picks only the relevant ones. This selection is quick and optimized, so you don’t waste time running unnecessary checks.
- Parallel Execution Model : it executes multiple scripts at the same time across different ports and targets. This parallel execution is a big reason why Nmap saves so much time compared to manual testing.
- Scripts Interaction with Target : Each script directly interacts with the target. It sends requests, observes how the system responds, and then analyzes that response. If something unusual or vulnerable is found, it reports it.
Flow of Execution
NSE also follows a flow of execution. Before scripts run, a small setup phase prepares the environment. Then comes the main execution phase where scripts actively test the target. Finally, after everything is done, the results are organized and presented in a clean, readable format.
Essential Elements of NSE
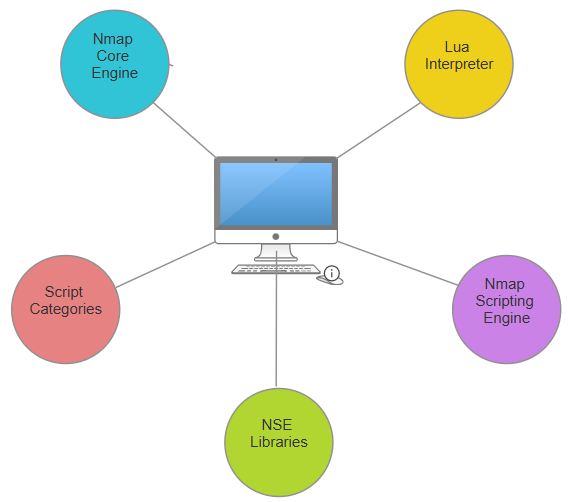
NSE is a framework composed of several closely related elements rather than a single feature:
- The Nmap Core Engine
It serves as the cornerstone.
- manages the host finding
- Scanning ports
- Identification of services
- Communication over networks
- NSE has no goals to strive for in the absence of the main engine.
- Lua Interpreter
Lua is a quick and lightweight programming language used to write NSE programs.
- Designed to be fast
- minimal use of memory
- Perfect for automating networks
NMAP scripting Engine
This is Execution layer. Decides when to run scripts, manage parallel execution and controls script dependencies.
NSE Libraries
Nmap Scripting Engine (NSE) libraries are Lua modules that extend script functionality for tasks like networking, parsing, and protocol handling.
- shortport: Defines port rules and service matching for script execution (e.g., shortport.http)
- smb: Handles SMB/CIFS protocol interactions, including enumeration and authentication.
- datafile: Loads Nmap data files for protocols, payloads, and match data.
- match: Provides pattern matching utilities for parsing responses.
- nmap: Core Nmap API for sockets, timing, output, and host/port info.
Script Categories
Nmap Scripting Engine (NSE) organizes scripts into categories to control execution based on risk, purpose, and scan type. These help users select scripts like –script discovery for targeted scans.
- brute: Performs brute-force
- discovery: Identifies hosts, services, and network details
- dos: Tests for denial-of-service vulnerabilities
- malware: Detects backdoors or infections
- safe: Low-risk scripts unlikely to harm targets.
- fuzzer: Sends malformed data to find bugs.
Commands and their output
nmap --script vuln 192.168.1.10Output
PORT STATE SERVICE
80/tcp open http
| http-shellshock:
| VULNERABLE:
| Shellshock vulnerability (CVE-2014-6271)
| State: VULNERABLE
| Risk factor: High
|
| smb-vuln-ms17-010:
| VULNERABLE:
| Remote Code Execution vulnerability in Microsoft SMBv1
| Risk factor: Critical
nmap -p445 --script smb-vuln* 192.168.1.20Output
PORT STATE SERVICE
445/tcp open microsoft-ds
| smb-vuln-ms17-010:
| VULNERABLE:
| Remote Code Execution vulnerability in Microsoft SMBv1
| CVE: CVE-2017-0143
| Exploit: EternalBlue
| Risk: CRITICAL
nmap -p80 --script http-enum 192.168.1.10Output
| http-enum:
| /admin/: Admin panel
| /backup/: Backup folder
| /phpmyadmin/: phpMyAdmin login page
Leave a Reply