How it works ?
SYN is a default scan type. It performs highly accurate and rapid scans, especially in environments that lack a firewall. As a result, it can probe a very large number of ports in a short amount of time, often within seconds. In addition, it executes a stealthy scan by generating minimal noise, which reduces the chances of detection.
This technique uses a “half-open” scanning method. In other words, it terminates the interaction before establishing a full TCP session. If a SYN/ACK packet is received in response, the port is marked as open. However, if an RST packet is received, the port is categorized as closed.
On the other hand, if a port fails to provide any response, it is classified as filtered. Similarly, if a port responds with an ICMP “unreachable” error (Type 3, Code 0, 1, 2, 3, 9, 10, or 13), it is also considered filtered.
Interestingly, if a port responds to a SYN packet without including the ACK flag, it is still marked as open.
Command & Output
SYN Scan Technique
nmap -sS scanme.nmap.org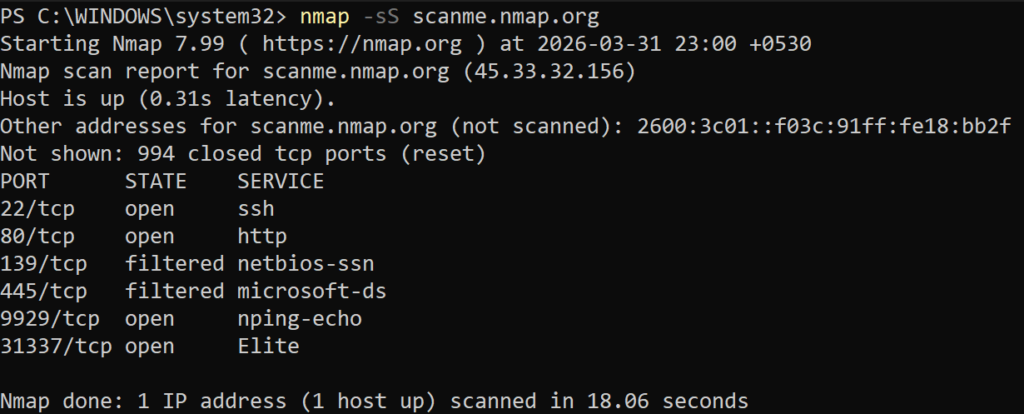
Port, State, Services Details
| PORT | STATE | SERVICES |
| 22/TCP | OPEN | SSH |
| 80/TCP | OPEN | HTTP |
| 139/TCP | FILTERED | NETBIOS-SSN |
| 445/TCP | FILTERED | MICROSOFT-DS |
| 9929/TCP | OPEN | NPING-ECHO |
| 31337/TCP | OPEN | ELITE |
Basic Details
Nmap scan report for scanme.nmap.org (45.33.32.156)
Host is up (0.31s latency).
Other addresses for scanme.nmap.org (not scanned): 2600:3c01::f03c:91ff:fe18:bb2f
Not shown: 994 closed tcp ports (reset)
Method : Decoy Scan
A decoy scan refers to scanning a target using randomly generated IP addresses, known as decoys. This technique, multiple fake IPs are used alongside your real IP. As a result, your actual IP address gets hidden among these decoys, making it difficult to identify the true source of the scan.
Random Decoy
nmap -sS -D RND:10 scanme.nmap.orgManual Decoy
nmap -sS -D 10.0.0.1,10.0.0.2,ME scanme.nmap.org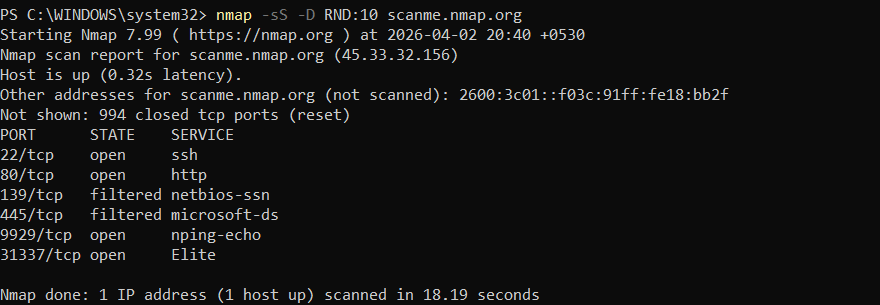
- -D : This calls the Decoy flag in command.
- RND:10 : It command decoy to generate 10 random IPs for spoofing.
- -ME : It specify your IP address.
- 10.0.0.1,10.0.0.2,ME : You can make your own order for decoys, this order is must important.
Port, State, Services Details
| PORT | STATE | SERVICES |
| 22/TCP | open | SSH |
| 80/TCP | open | HTTP |
| 139/TCP | filtered | NETBIOS-SSN |
| 445/TCP | filtered | MICROSOFT-DS |
| 9929/TCP | open | NPING-ECHO |
| 31337/TCP | open | ELITE |
Fragment packet Technique
8-Byte Fragments
nmap -sS -f 45.33.32.156Fragmentation scan techniques may work against weak IDS. However, modern firewalls and systems like Snort can easily detect such patterns, making them less effective.
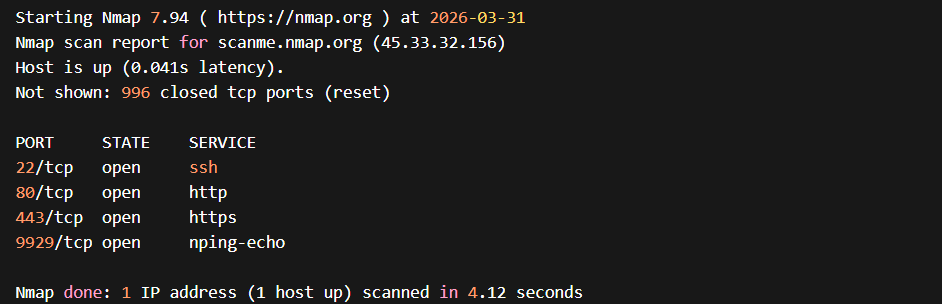
- -f : It flag command for fragment packets. This actually sends the fragments of size 8 byte each.
Port, State, Services Details
| PORT | STATE | SERVICES |
| 22/TCP | open | SSH |
| 80/TCP | open | HTTP |
| 443/TCP | open | HTTPS |
| 9929/TCP | open | NPING-ECHO |
16-Byte Fragments
nmap -sS -ff 45.33.32.156Using 16-byte fragments makes detection by IDS more difficult. The Nmap SYN packet is split into small 16-byte fragments, which can also be used to test firewall behavior.
- -ff : It flag the fragment of 16 byte.
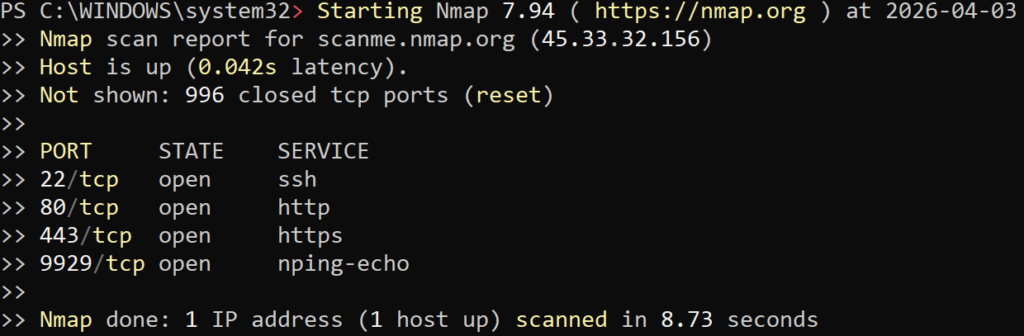
Table : Port, State, Services Details
| PORT | STATE | SERVICES |
| 22/TCP | open | SSH |
| 80/TCP | open | HTTP |
| 443/TCP | open | HTTPS |
| 9929/TCP | open | NPING-ECHO |
Fragment MTU (Maximum Transmission Unit)
nmap -sS --mtu 24 45.33.32.156- The
--mtuoption sets the fragment size during a SYN scan. The size is specified in multiples of 8 bytes (e.g., 16, 32, 64) and can go up to around 1480 bytes.
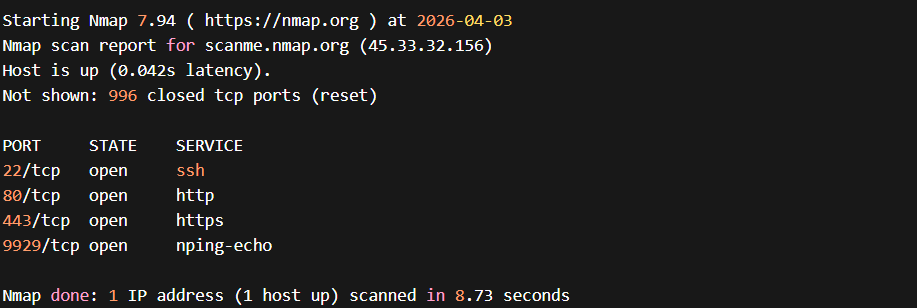
Table : Port, State, Services Details
| PORT | STATE | SERVICES |
| 22/TCP | open | SSH |
| 80/TCP | open | HTTP |
| 443/TCP | open | HTTPS |
| 9929/TCP | open | NPING-ECHO |
SYN Scan with DNS Port
nmap -sS --source-port 53 45.33.32.156The --source-port option forces packets to appear as if they originate from port 53 (DNS). As a result, the traffic may look like legitimate DNS communication, which can sometimes be trusted by weak firewalls or IDS rules.
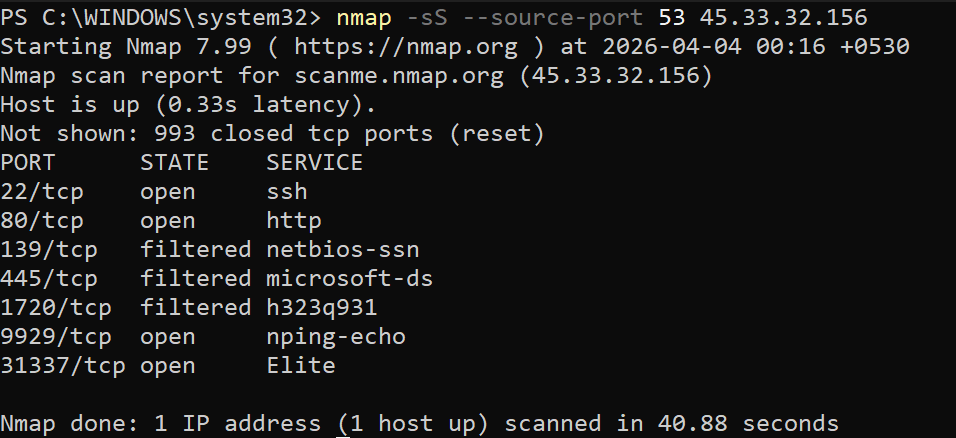
Port, State, Services Details
| PORT | STATE | SERVICES |
| 22/TCP | open | SSH |
| 80/TCP | open | HTTP |
| 139/TCP | filtered | NETBIOS-SSN |
| 445/TCP | filtered | MICROSOFT-DS |
| 1720/TCP | filtered | H323q931 |
| 9929/TCP | open | NPING-ECHO |
| 31337/TCP | open | ELITE |
Leave a Reply